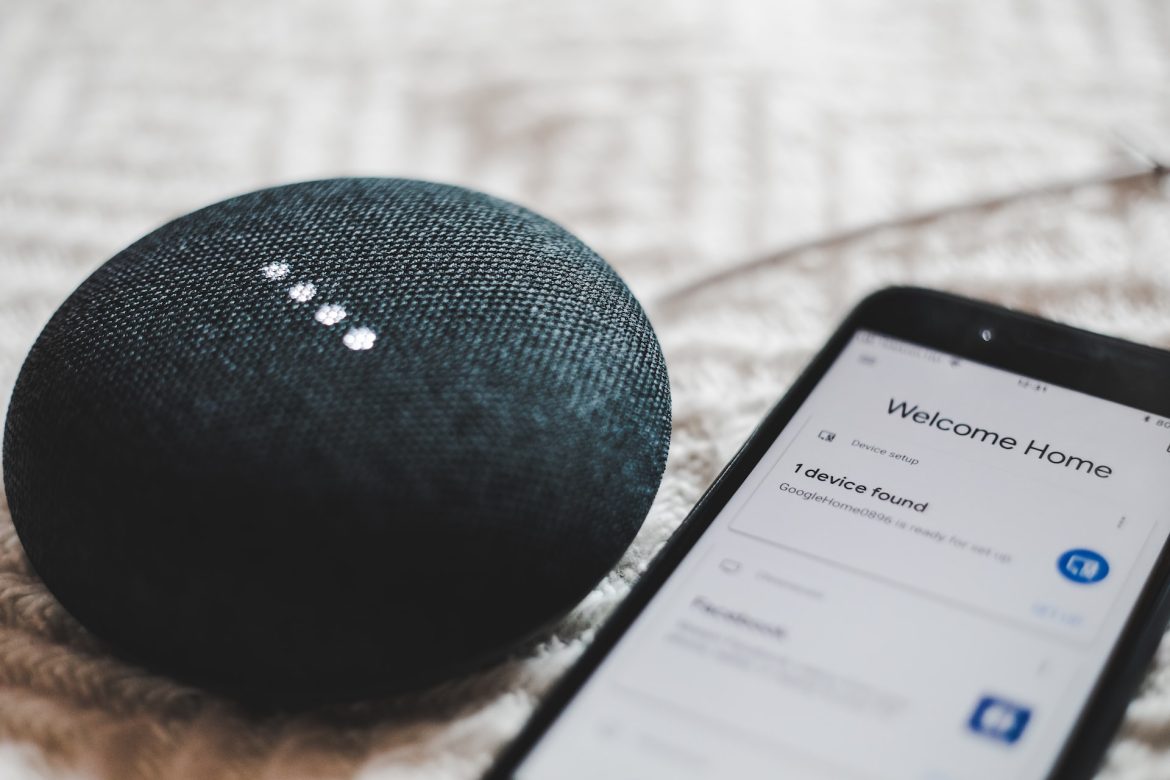
What is IoT?
The Internet of Things (IoT) represents a set of interconnected devices (identifiable physical objects) able to interact with themselves, among themselves, with their environment and come to different decisions in the capacity that their artificial intelligence allows it. Using controllers and nodes, these devices have the ability to collect and share gathered data among themselves and make autonomous decisions based on it. The following are some characteristics of these “things”:
- Fully embedded
- Focused on real-time data collection
- Utilising a variety of networks
- Having ongoing or sporadic connectivity, necessitating the need for time-stamped data storage
- Capable of measuring physical parameters
- Ability to make judgments based on the information gathered, enabling centrally-automated decision-making.
The benefits of IoT
Before we get to the potential issues regarding IoT, we’ll cover the benefits in different fields provided by IoT. The automation of processes along with seamless data integration and timely reaction is what specialised IoT companies have to offer to almost any field of human endeavour. In the field of industry, IoT provides optimal customisation of services and products, based on the data collected from customers. It also enables manufacturers to better understand the needs of the customers and make timely adjustments. In healthcare, the contribution of IoT is essential in real-time medical data monitoring, providing automated feedback to patients and supplying the medical staff with relevant data. Transportation is another field in which the assistance of IoT is invaluable, allowing for package monitoring to track the location, environmental conditions and possible meddling with cargo. Other useful IoTs are commercial and consumer.
The building blocks of an IoT include the hardware and the software, connectivity and data, along with security. The last element overarches those before it and is the one with which issues and challenges are most likely to arise.

The issues with IoT
As IoTs are not just devices but an internet of devices, there is a number of points where issues can arise. A framework of trust provides users with the confidence that the exchange of data and services takes place in a secure environment. Some of the most frequent weaknesses of an IoT entail issues related to the security of the web interface, network services, cloud interface, and mobile interface, along with privacy concerns, and concerns about transport encryption and software. There are, of course, questions regarding the physical security of the devices as well. But still, one of the most pressing issues is the issue of authentication and authorization.
Authentication issues
A malicious device inserted in an IoT network could wreak havoc on the whole system so taking additional precautions and safety measures against malfunctions and cyberattacks is recommended. There is a variety of approaches someone could take in an attempt to compromise IoT including masquerade attack, forging attack, DoS attack, man-in-the-middle attack, physical attack, guessing attack and routing attack. Attackers use a wide variety of tactics, including forging users’ identification, replicating a system component, intrusions on network traffic between devices, and choking the network by overburdening it with information and eventually breaking in. This could cause issues with identity and access management, data and network security, compliance with regulations and the sharing of data.
Identity and access management (IAM)
IAM controls which devices have access to the network and what operations they are allowed to perform. It also specifies how devices or individuals are recognised as authentic and authorised users. Numerous industrial IoTs are susceptible to attacks targeting faults in IAM, so no organisation is safe without the most cutting-edge identity and access management precautions. Without the security of the main network, numerous industrial IoT could fall victim to cyberattacks. Through cracks in the IAM, a hacker could infiltrate the main server and steal valuable information. Devices with faulty IAM are also prone to misleading communications from malfunctioned servers, which can in turn cause them to act in ways they are not meant to.
Security of data and network
IoTs are hubs of data, with information constantly circulating to and from the home network and the various interconnected devices. The home network uses the data it receives to optimise the decision-making process and to better monitor the system. It then issues orders to the devices and keeps them up to date. Therefore, an authentication problem could prove fatal for the flow of information, as there would be no way to verify how reliable the data is. Furthermore, in a compromised network, data is prone to theft and unauthorised access. With authentication effectively gone, a hacker could also use a compromised device to spread malicious software like a virus.
Compliance with regulations
With many global and industry-specific regulations, companies are obligated to manage any personal data in a strict and safe way. A breach into the data network could potentially compromise personally identifiable information as well as the reputability of the organisation. It could also incur fines due to a breach of regulations.
Sharing of data
Carefully scrutinising and sharing data between organisations and third-party contractors is a key asset of IoTs, yet it is becoming increasingly difficult to utilise this function safely, as authentication issues bring the question of privacy and safety to the fore.
The solution
As traditional measures have proved insufficient when it comes to keeping an IoT system safe, a more lightweight authentication system has been adapted to the way IoTs function. Numerous solutions have been proposed including cryptographic, password-based, biometric, token-based, and multi-factor authentication, each with its own unique benefits and drawbacks. Their goal is still the same, however, and that’s keeping the IoT network safe from breaches and malicious intent. Recommendations have also been provided for those employed in companies utilising IoT networks and include frequent scrutiny, paying attention to digital security hygiene and minimising exposure of the key factors in authentication i.e. passwords. The overarching advice is to stay vigilant when it comes to possible data breaches and cut the problem at the root as soon as possible so it doesn’t have a chance to spread and cause chaos to the whole system.
With the expansion of IoT networks sure to continue, there will also be the need for an ever more robust, safe and adaptable way to keep them secure and free of breaches and attacks, while complying with regulations and keeping personal data safe.